Introduction
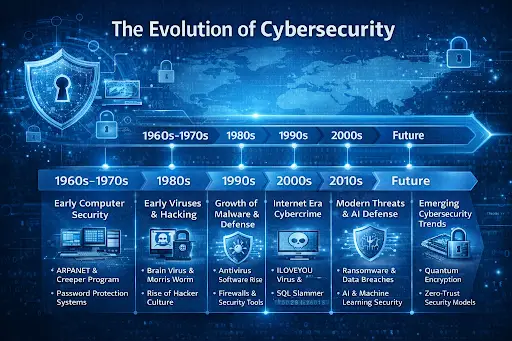
The History of Cybersecurity reflects the ongoing struggle to protect digital systems as technology evolves. As computers became more powerful and connected through networks, protecting data and information systems became increasingly important. Cybersecurity focuses on defending computer systems, networks, and digital information from unauthorized access, cyber attacks, and data breaches.
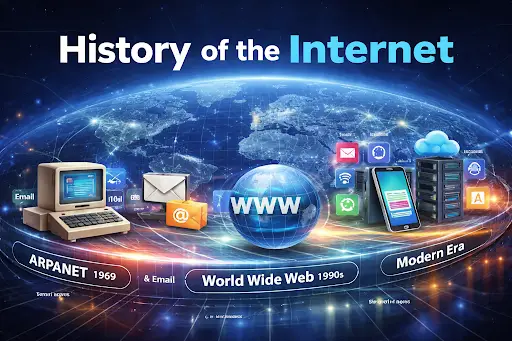
In the earliest days of computing, security was not a major concern because computers were isolated machines used mainly by researchers and government institutions. However, once networks began connecting computers across different locations, new risks emerged. Hackers, computer viruses, and other forms of malware quickly exposed weaknesses in digital systems.
Over time, the development of cybersecurity tools and strategies became essential to protect modern infrastructure. The evolution of cybersecurity shows how digital defense systems have continuously adapted to new threats. From basic password protection to artificial intelligence–powered threat detection, cybersecurity now plays a central role in the global technology ecosystem.
Early Computer Security Foundations (1960s–1970s)
The origins of cybersecurity began during the early decades of computing in the 1960s. At that time, computers were large mainframe systems used by universities, research labs, and government organizations. These machines were extremely expensive and centralized, meaning multiple users accessed them through shared terminals.
Because several users relied on the same computer, early security systems focused on controlling access. Password authentication became one of the first security measures used to restrict who could use a system.
During this period, the development of ARPANET introduced new security challenges as computer systems began communicating across networks, a transformation later explored in the history of computer networking.
As network communication increased, researchers began to recognize the possibility of malicious programs spreading between systems. In 1971, a program known as Creeper became one of the earliest examples of self-replicating software. Creeper moved between computers on ARPANET, displaying a message but causing no direct damage.
To remove the program, developers created Reaper, which searched for and deleted Creeper. This program is often considered one of the earliest examples of antivirus software. These events represented the first signs that computer systems would need protection from digital threats.
The Rise of Computer Viruses and Hacking (1980s)
The 1980s marked a major shift in the cybersecurity timeline as personal computers became widely available. With more individuals gaining access to computers, malicious software and hacking activities began to increase.
One of the first widely recognized computer viruses was the Brain virus, discovered in 1986. Created by two programmers in Pakistan, the virus infected floppy disks and spread between computers. Although the creators initially designed it to monitor unauthorized copying of software, the program demonstrated how easily malware could propagate.
At the same time, hacker culture began emerging in the technology community. Some hackers explored computer systems out of curiosity or intellectual challenge, while others sought unauthorized access for personal gain.
A major cybersecurity incident occurred in 1988 when the Morris Worm spread across the early internet. The worm infected thousands of computers and caused widespread disruption. The event revealed serious weaknesses in network security and led to the creation of the Computer Emergency Response Team (CERT) to respond to cybersecurity incidents.
These developments highlighted the growing importance of digital defense systems and helped shape the early history of cyber attacks.
Growth of Antivirus and Security Technologies (1990s)
The 1990s saw rapid expansion of the internet and personal computing, which dramatically increased cybersecurity risks. As more people began using computers for communication and business, cyber threats became more frequent.
Malware evolved beyond simple viruses. Macro viruses began exploiting vulnerabilities in software programs like word processors and spreadsheets. These viruses often spread through infected email attachments.
One of the most famous examples was the Melissa virus, discovered in 1999. The virus spread rapidly through email systems, infecting thousands of computers and forcing major organizations to temporarily shut down their email services.
During this time, the antivirus industry grew quickly. Software companies developed security programs designed to detect and remove malicious code before it could damage systems.
Security technologies such as firewalls and intrusion detection systems were also introduced. These tools monitored network traffic and helped prevent unauthorized access to computer systems.
As digital communication expanded, organizations began realizing that protecting networks and data would become a long-term challenge.
Internet Expansion and Cybercrime (2000s)
The early 2000s brought explosive growth in internet usage. Businesses, governments, and individuals increasingly relied on online systems for communication, commerce, and data storage. This expansion created new opportunities for cybercriminals.
One of the most destructive cyber incidents of this period was the ILOVEYOU virus, which spread through email attachments and infected millions of computers worldwide. The attack caused billions of dollars in damages and demonstrated how quickly cyber threats could spread across the global internet.
Another significant attack was the SQL Slammer worm in 2003. The worm exploited a database vulnerability and spread across the internet within minutes, disrupting thousands of servers.
These attacks marked the rise of organized cybercrime, where attackers targeted financial institutions, businesses, and government agencies for profit.
In response, cybersecurity technologies improved rapidly. Encryption methods became stronger, security protocols were enhanced, and organizations began implementing more advanced network security strategies.
Modern Cybersecurity Evolution (2010s)
During the 2010s, cybersecurity became one of the most important concerns in global technology infrastructure. Businesses began moving services online, and cloud computing platforms became essential for data storage and application deployment.
However, as digital infrastructure expanded, cyber attacks also became more sophisticated. Ransomware attacks became one of the most dangerous threats. These attacks encrypt an organization’s data and demand payment for its release.
Large-scale data breaches affected major corporations and government institutions, exposing millions of user records and sensitive information.
To combat these threats, cybersecurity technologies evolved significantly. Advanced systems began using machine learning and artificial intelligence to detect suspicious activity and prevent attacks in real time.
The growing use of cloud services also introduced new security challenges, especially as organizations began adopting platforms described in the history of cloud computing.
Modern Impact of Cybersecurity
Today, cybersecurity plays a critical role in protecting global digital infrastructure. Nearly every industry relies on secure information systems to operate effectively.
Cybersecurity helps protect:
- financial transactions
- personal information
- healthcare records
- government systems
- online communication platforms
Modern cybersecurity strategies rely on multiple layers of protection, including encryption, authentication systems, security monitoring, and automated threat detection.
As businesses increasingly rely on digital services, cybersecurity has become a core component of business operations, national security, and personal privacy protection.
Future Outlook of Cybersecurity
The future of cybersecurity will be shaped by emerging technologies and increasingly complex cyber threats. As artificial intelligence, cloud infrastructure, and connected devices continue expanding, new vulnerabilities will inevitably appear.
One major development is the zero-trust security model, which assumes that no user or system should automatically be trusted. Instead, every request for access must be continuously verified.
Artificial intelligence will also play a growing role in cybersecurity. AI-powered systems can analyze large volumes of data to detect suspicious behavior and respond to threats faster than traditional security tools.
Another emerging challenge involves quantum computing, which could potentially break many existing encryption methods. Researchers are already developing quantum-resistant cryptographic systems to address this potential risk.
As digital systems become more advanced, cybersecurity will remain essential for maintaining trust and stability in the digital world.
FAQ
What is the history of cybersecurity?
The history of cybersecurity began in the 1960s with early computer security methods such as password protection and access control systems. It evolved as cyber threats like viruses and hacking appeared.
When did cybersecurity start?
Cybersecurity began during the early era of networked computing in the late 1960s when researchers started addressing security vulnerabilities in shared computer systems.
What was the first computer virus?
One of the earliest known computer viruses was the Creeper program in 1971. It spread across ARPANET systems but was not designed to cause harm.
Why is cybersecurity important today?
Cybersecurity protects sensitive information, prevents cybercrime, and ensures the safety and reliability of digital systems used worldwide.
How has cybersecurity evolved over time?
Cybersecurity has evolved from simple password protection to advanced technologies such as encryption, intrusion detection systems, and AI-powered threat monitoring.
What are common types of cyber attacks?
Common cyber attacks include malware, ransomware, phishing, denial-of-service attacks, and data breaches.
Conclusion
The History of Cybersecurity shows how digital protection has evolved alongside advances in computing technology. From early mainframe security systems to modern AI-powered threat detection, cybersecurity continues to adapt to an ever-changing landscape of digital threats. As technology continues to advance and cyber risks become more complex, strong cybersecurity practices will remain essential for protecting the world’s digital infrastructure.